You Still Need to Back Up Your Microsoft 365 Data
You Still Need to Back Up Your Microsoft 365 Data
Multiple organisations have settled on cloud-based Software-as-a-service (SaaS) solutions from the Microsoft 365 (M365) family of products.
This is understandable as M365 provides rich applications and services that are easy to commission and onboard users without any on-premise infrastructure management.
Do you need to back up Microsoft 365 data, such as the emails in Office 365? It’s a question that’s often asked. And it’s a question that’s frequently answered in contradictory ways. Let’s not bury the lede — the answer, as far as we are concerned, is an emphatic yes. It’s your data in M365, and you are responsible for it. Microsoft delivers some protections via SLAs, site mirroring, and retention policies. But these are not backups in the traditional sense, and if you have to produce data for regulators at some point or for any other reason, you may discover they’re not good enough.
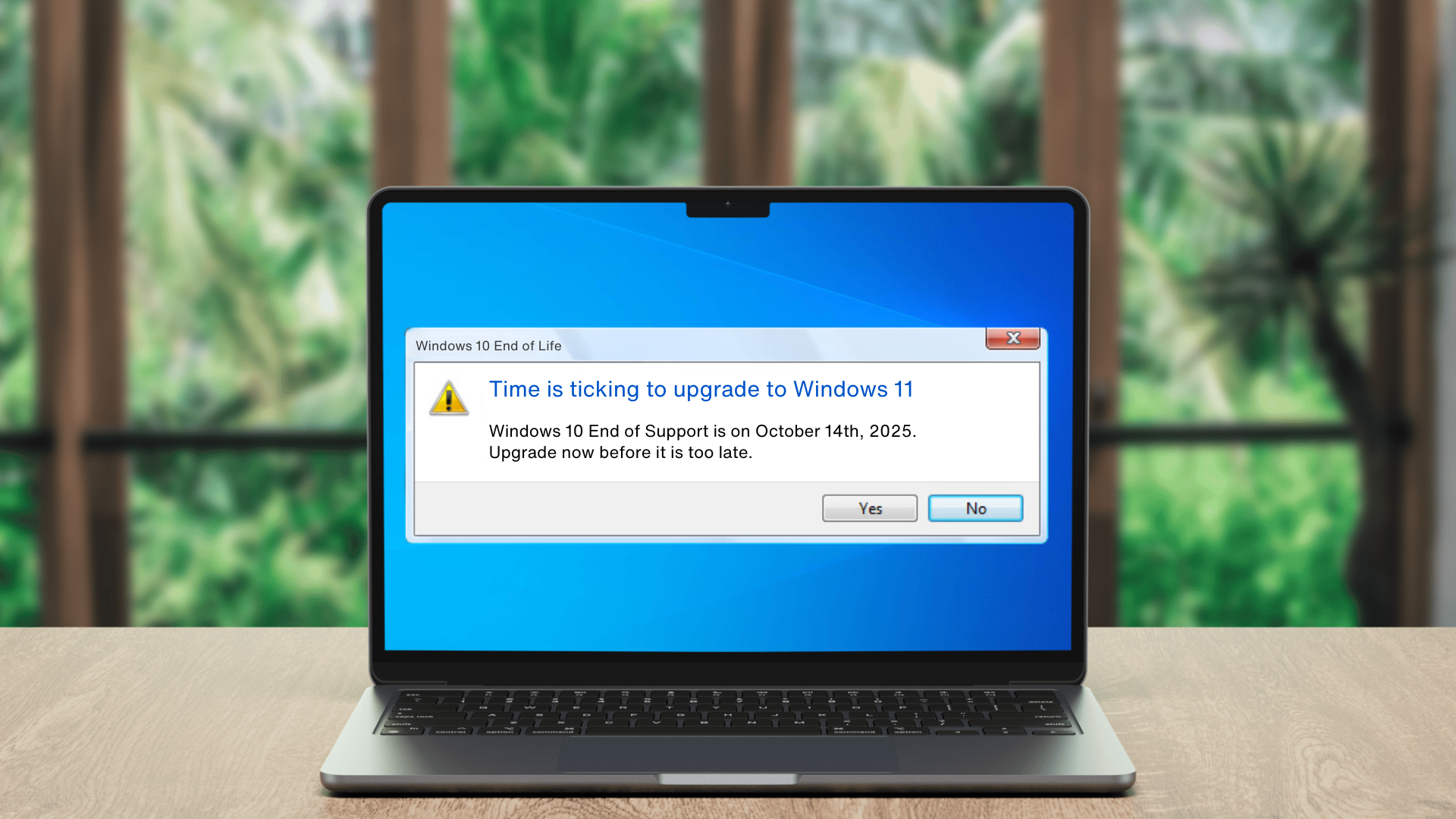
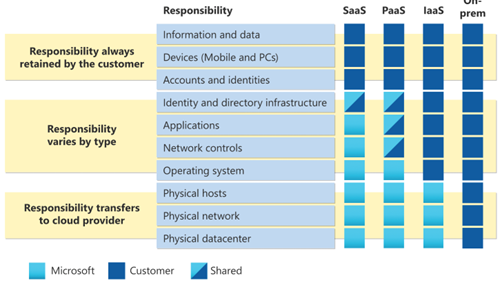
One aspect of M365 and other cloud services from Microsoft that often surprises people is that having your data in M365 does not remove your responsibility for backing it up. Microsoft operates its cloud-based services on a shared responsibility model, and for data stored in its SaaS solutions like M365, the responsibility for data backup and integrity resides with the organisations using M365. Image 1 shows a table of responsibilities taken from Microsoft’s Shared responsibility in the cloud document on the Microsoft Learn site.
Figure 1: Microsoft and Customer Responsibilities in the Microsoft Cloud. (Retrieved on May 1st 2024, from https://learn.microsoft.com/en-us/azure/security/fundamentals/shared-responsibility.)
In this blog, we outline why storing your data in M365 doesn’t mean you can forget about backups. Thankfully, many options are available to deliver backups for Microsoft 365 data. We encourage you to contact your current account manager in Infinity IT to discuss backing up your M365 data. You can also use our Contact Form to start a conversation.
M365 Data Is Still Vulnerable to Loss
Microsoft provides replication and retention policies to deliver service availability SLAs in M365. You can even specify that data in M365 should not get deleted. However, just because the data is flagged to be retained in M365 and replicated across multiple cloud data centres does not mean it’s safe from accidental damage, cyberattacks, or malicious insider activity. Issues that can cause data loss include:
⁃ Human Error - Data is at risk of being lost if it is deleted or overwritten, and this does not get discovered within the M365 retention period.
⁃ Malicious damage - Sometimes, staff intentionally destroy or corrupt data, which can result in permanent data loss if not discovered quickly and no backups are available.
⁃ Synchronisation errors - When using M365, data is regularly exchanged between the platform and end-user devices. Due to the high number of devices and frequency of data exchanges, some errors are likely to occur. Even a few errors that result in data loss or corruption could negatively impact operations or decrease staff productivity.
⁃ Cyberattacks - It’s important to note that M365 can be vulnerable to cyberattacks, data breaches, and loss due to criminal activities such as ransomware. If you rely solely on Microsoft for data retention, your business may suffer significant losses and harm to its reputation. Taking proactive measures to safeguard your data against any potential incidents is crucial.
⁃ Natural disasters - There is a possibility, albeit small, that a catastrophe could cause a disruption in your access to M365 for several days or more. If you don’t have a backup of important data stored elsewhere, your organisation might be unable to function properly until M365 access gets restored.
Microsoft's Native Data Retention Features
Now that we’ve highlighted how you can lose M365 data due to corruption or deletion, let’s outline the features Microsoft includes to deliver partial data security, compliance, and availability.
Datacentre-to-Datacentre replication - Microsoft replicates data across multiple M365 data centres. However, it is important to note that this replication does not serve as a replacement for a dedicated backup solution. It cannot protect against some of the common data loss issues, such as accidental deletion or ransomware attacks. You still need a proper backup solution for comprehensive data security.
Retention policies - M365 provides retention policies that enable organisations to comply with regulations and internal policies by retaining or deleting content after a specific period. However, although these retention policies are helpful, they are not fool proof. Mistakes can occur when configuring retention policies, which can result in data loss. System Admins are susceptible to making errors, just like any other person.
Litigation hold - M365 allows organisations to put content on hold for legal cases, eDiscovery, or internal investigations. However, backups are vital to complement M365 legal holds to protect against user error or malicious deletion to preserve content needed for investigations.
Archive mailbox - Exchange email in M365 provides an archive mailbox with extra storage space to archive emails. However, this archive is subject to the same data loss risks as the primary mailbox, including accidental deletion and user error.
Microsoft Defender for Office 365 - While Microsoft Defender for Office 365 helps protect email with advanced protection against phishing, business email compromise, ransomware, and other cyber threats, it is not a substitute for backup. Backups are the ultimate safety net to protect your organisational data and shared knowledge from accidental and malicious damage.
Proper Backups are required to Deliver Compliance
Regulations such as GDPR require organisations to ensure data protection. This responsibility includes securing data while it is being stored, transmitted over networks, and even backed up. Hence, when choosing a backup solution to safeguard data, it is crucial to select a solution that allows the selection of target locations that align with each organisation’s regulations. For instance, when data must remain within the EU region to adhere to regulations.
Quick Data Recovery is Vital
One of the most important aspects of data backup or retention policies is the ability to quickly recover vital emails or other information when needed. Often in pressured situations if a disaster or cyberattack has occurred. Even if you believe that Microsoft’s built-in data protection features are good enough (trust us - they really aren’t), experience shows that recovery of data using the native M365 tools can be slow and cumbersome. In some cases, restoring data to its original state may be extremely difficult, particularly across different user accounts.
Having a robust third-party backup of your M365 data, especially emails, ensures you can meet your Recovery Point Objectives (RPO) and Recovery Time Objectives (RTO), minimising downtime and enabling a swift return to normal operations after an incident.
There is no doubt that Microsoft’s built-in M365 features provide some functionality for data security, compliance, and availability, but they do not replace the functionality in a comprehensive backup solution. As demonstrated in Figure 1 where Microsoft clearly states that the responsibility for information and data resides with their customers - the organisations that use M365 (and other Microsoft cloud services).
As the data owner, you are responsible for managing the risk of data loss due to issues like accidental deletion and ransomware. By implementing a dedicated backup solution for Microsoft 365, you can ensure that your critical data is always protected and recoverable, enabling business continuity and peace of mind in the face of ever-evolving threats. The Microsoft M365 and Azure experts in Infinity IT are here to help you choose, implement, and operate a backup solution that protects your M365 data.
Your IT Upgrade Starts Here: Contact Us for a Complimentary Assessment
Contact Us
Your IT Upgrade Starts Here: Contact Us for a Complimentary Assessment
Contact Us